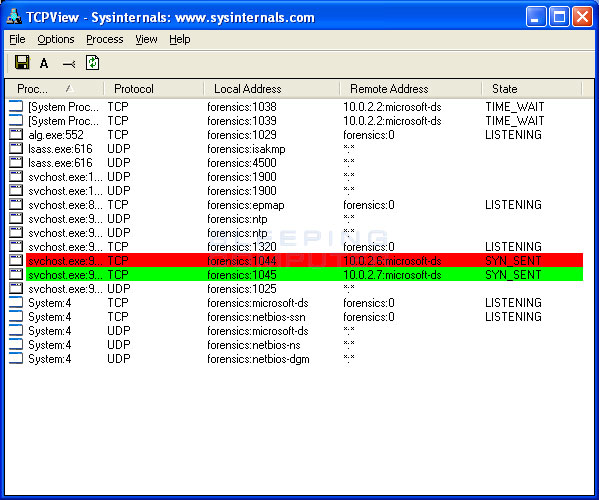
Botnet spoofing: fighting botnet with itself - Xiang - 2015 - Security and Communication Networks - Wiley Online Library

How a malicious server can update the firmware of a victim's router.... | Download Scientific Diagram

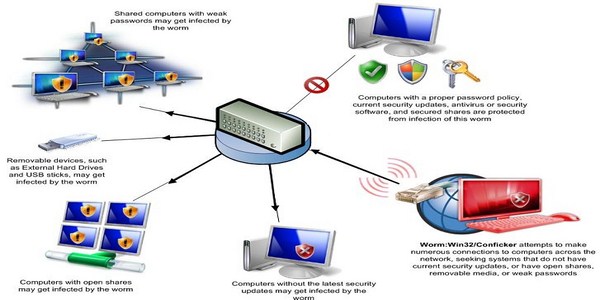
Eddy Willems on Twitter: "Surprisingly #conficker #mirai #vpnfilter are very prominently found in Belgium cfr Miguel De Bruycker of #CCB https://t.co/TQbWHSGEnB" / Twitter



/cloudfront-us-east-1.images.arcpublishing.com/gray/H625APTEBJCF7C5NR4PHG25M7A.jpg)

/cloudfront-us-east-1.images.arcpublishing.com/gray/H625APTEBJCF7C5NR4PHG25M7A.jpg)